We have previously (June 2012) discussed Mobile Device Management (MDM) as part of the emerging mobile cloud ecosystem in the enterprise area. A companion area that is growing up is MAM. While some observers have written about a battle between these two disciplines, in our view they are largely complementary and address somewhat different issues. We have also previously mentioned that some companies – Antenna Software is an example – see a strong link between their MADP (mobile apps development platforms) and MAM (see our commentary on Antenna Software, June 2012.)
AppCentral
AppCentral is one of the leaders in MAM. Founded as a provider of custom apps in 2007, the company turned to providing an enterprise app store as it realized that the issue of controlling apps was growing in magnitude. Over time this has grown into an expanding MAM platform and solution. In October 2012, Good Technology, a prominent player in MDM, announced that it was acquiring AppCentral.
The company’s solution is illustrated in the following diagram. Basically the company offers: “a cloud-based, custom- branded enterprise app storefront and management console” shown on the left side of the diagram. This provides administrators with easy tools for controlling availability to apps, providing for security and other policies. The company’s solution currently applies to apps on iOS, Android, and BlackBerry devices.
[lightbox type=”image” src=”https://www.mobilecloudera.com/wp-content/uploads/2012/12/mob-app-mgt.jpg”]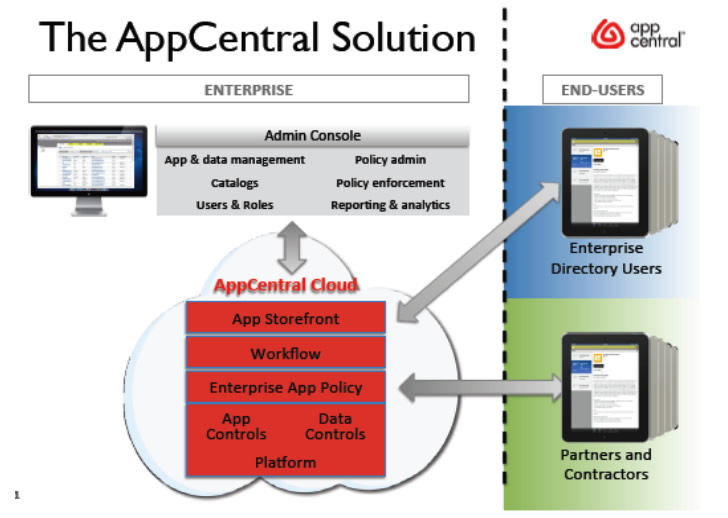 [/lightbox]
[/lightbox]
Among the key strengths in its solution that AppCentral points to are the fact that at the time the administrator uploads an app (whether it is from an outside store or a proprietary company app) the AppCentral cloud “wraps” a policy engine into the app. This wrapping technology is branded as AppGuardian by the company. It allows for functions such as wiping apps and data from lost or no longer qualified devices; enforcing security rules; and updating, so that all devices using the app will only be enabled if they have the latest version of controls.
AppCentral points to other strengths of its approach as being that its architecture has been designed assuming that there will be multiple mobile OSs that must be accommodated and also that is designed not just to assist IT departments, with their emphasis on security, but also to enable LOBs and provide the most positive user interface and experience.
In a major product extension, the company in June 2012 announced an upgrade of its platform to cover, not only company employees, but also contractors, business partners and distributors. This is pointed to as a significant advantage of MAM over MDM, since enterprises cannot generally obtain any control over devices of outside parties, but can through MAM platforms exert control of third parties’ uses of their applications.
The company charges a price per user, which declines on volume, from $5 per month to $2 per month. It stated that a 4,000-user installation would cost about $3 per month and above 10,000 users, the charge would be $2 per month.
AppCentral’s current experience with its customer base is enlightening. The company estimates that about one-half of the interest in its platform is coming from IT departments in enterprises and one-half from lines of business (LOB) executives. When the orders actually come from the LOBs, it finds that about half of these are then handed over to IT to administer the solution, while the LOBs in about half the cases administer control over the platform within their own area of the organization.
While initially customers were having the solution installed on premises, today 90% of its clients use it through the cloud. The company currently maintains its cloud on Amazon’s platform.
The company believes that MDM is currently complementary to MAM. It estimates that about 90% of its customers also have MDM systems. It points out the difficulties in reaching a comprehensive solution with MDM, since it does not reach partners’ devices, and also notes that in some areas, e.g., the EU, protection of individual user’s privacy rights may impede use of MDM systems
As for the actual future of devices and apps in the enterprise area, AppCentral believes that the key for device makers is whether the individual user “cherishes” the device, meaning that it is a device that they choose to carry with them. It is finding a proliferation of video augmented apps that are designed for use on iPads. In addition, it mentions that a leading customer, Mitsubishi is using augmented reality (AR) in collaboration with customers in the field.
It finds, on a more basic level, that many accounts start with fairly simple apps, such as converting paper price lists to an excel app that can be continually updated. As they progress, the typical enterprises design and build their own custom apps. A big opportunity for the company is represented by the LOBs who design apps that are intended for distribution outside their enterprise and who therefore require application control software and platforms.
Other MAM Companies: Symantec/Nukona
Symantec, a leader in security software, states that, based on its own survey, 59% of enterprises are now making line-of-business applications accessible from mobile devices. It also points out that its customers view mobile as their biggest area of risk in managing their corporate information security.
The company has made number of significant moves to address this issue, including the MAM and MDM areas. In March 2012, Symantec acquired Nukona, a leading MAM provider. Earlier in 2012 Symantec acquired MDM provider, Odyssey Software. So the company is attacking mobile security from a number of directions.
Nukona’s system includes an enterprise apps store and a “policy manager” which Nukona states, “can wrap apps in a management layer that allows IT to apply security policies for purposes such as authentication, enforcing encryption or setting restrictions.”
Nukona presents the example of an employee with two devices, one supplied by the company and one that is personal. It describes the administration of its system, which it calls App Center, as:
User credentials may be tied to your identity infrastructure (e.g. Active Directory)
Create relevant corporate policies
These dictate whether user authentication, encryption, offline access, etc. is required or allowed for each category of app
Apply the relevant policy to an app before distribution
If no specific policy is applied the corporate default will be used
Determine which users or groups of users will be allowed to access the app and will receive notifications of its availability
That’s it. You’re back in control
Mocana
Mocana has a specific focus on mobile and other non-PC device security. “Mocana is developing the industry’s only device-independent Smart Device Security platform that secures all aspects of IP addressable devices as well as the information, applications and services that run on them.”
One of its products is Mobile App Protection which: “Wraps fine-grained app-level DLP, VPN, and access & usage controls around individual mobile apps.” As with other MAM providers, Mocana identifies the problem for enterprises as being that MDM, while it can protect the corporation by managing devices that are within corporate control, falls short when it comes to BYOD or devices that are totally outside the company.
As the company states:
“For many, the big question is how to balance the need for information security and the protection of corporate data and assets against the privacy of personal information on an employee’s own device—all while preserving the user experience. These questions are poorly answered by blunt responses like ‘wipe the device’ or ‘revoke the device’s credentials.’ Today’s IT needs more fine-grained control, particularly because the target device does not necessarily belong to the enterprise. The corporate boundary is becoming increasingly fuzzy as affiliates, partners, contractors, and even end customers are all recipients of the enterprise’s data— often on devices the enterprise does not own.”
Apperian
Apperian claims that it “created the first Mobile Application Management cloud platform,” which it calls Enterprise App Services Environment (EASE). It emphasizes the three-stage process of: 1) creation of transformative mobile business apps; 2) creation of an enterprise app store; and 3) management of the life cycle of the apps. It also emphasizes that it provides “app ratings and crowd sourcing” as built-in features of its platform, so that administrators can be aware of users’ level of satisfaction with specific apps. The company counts a customer base of over 100,000 users.
Apperian listed the attributes of its latest EASE release (May 2012) as follows:
Inspect – Malware detection, automation, validation and signing services
Protect – Geo-fencing, data encryption, app delete and device level management
Extend – Dynamic policy, remote control, silent install, private app network and single sign-on
Personalize – Role-based apps, custom branding, targeted content and recommendations
Analyze – Adoption and usage of apps, compliance reports, app inventory and performance
Engage – Sharing and liking apps, app rating, crowdsourcing and gamification features
Apperian supports mobile security features of Mocana (as well as those of mFormation Technologies.)
Outlook For MAM
The argument about MAM versus MDM, to the extent it persists, appears to be based on the following key points:
1. If your control is exerted at the apps level, you can control policies and usage related to any given app, regardless of who owns the device; thus it enables extending the enterprise’s scope to outside parties.
2. MAM appears to be more of a response to the BYOD phenomenon and the idea that devices may widely be used for both business and personal purposes, while MDM grew up more focused on an environment where companies were controlling the issuance of devices and the purposes for which they were being used.
The MAM people have made a convincing case that there are important advantages to maintaining distribution (publication), control and management of the wide range of mobile apps through a centralized platform (which will undoubtedly migrate to the cloud.)
However, there are already signs of a crossover between these two areas, MDM and MAM, and they hardly seem to be mutually exclusive for the long run. As one example, MobileIron, which we discussed in our prior report as a leading MDM provider, offers a “built-in Enterprise App Storefront.” It does not appear that the claimed features for the MobileIron storefront are currently as advanced as, for example, the AppCentral platform. For example, MobileIron states that administrators can “recommend external applications” and tell users where to find them, while the AppCentral platform provides for administrators to obtain the outside apps and incorporate them into the storefront.
It would appear that there will be movement in the following directions:
1. Combined MDM/MAM platforms
2. Mergers of MDM and MAM providers: This was strongly reinforced by Good Technology’s announced purchase of AppCentral in early October 2012.
3. Acquisitions by larger security and other companies of both MDM and MAM providers. This is already under way, witness the Symantec acquisitions discussed above, and we would expect this to accelerate.